Or use your brothers laptop, lol. That's another nice thing about Duck Duck Go browser. It both blocks many trackers and cookies and also deletes the ones that are allowed to load out of necessity for site functionality. Does this every time you close the browser.Lesson here.
Clear your cookies before and after a visit to pornhub. lol
Navigation
Install the app
How to install the app on iOS
Follow along with the video below to see how to install our site as a web app on your home screen.
Note: This feature may not be available in some browsers.
More options
Style variation
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Internet and computer security
- Thread starter Murray20c8
- Start date
For anyone wondering what all the fuss is about Artificial Intelligence and want to get an understanding of the basics and what all of the terms mean such as inference, LLM's , data sets and centers , etc , Acadia University in Wolfville NS are offering a free course online . Simply create a username and password and you get free access. Its called " Introduction to AI Literacy " . AI is considered to be the most " disruptive " technology since the PC or even the World Wide Web itself. This is going to change everything regardless of what we think about it. Good to stay informed!
 explore.acadiau.ca
explore.acadiau.ca
Introduction to AI Literacy
 explore.acadiau.ca
explore.acadiau.ca
One for Murray . You have been asking for this and it looks like its in the works.....
A long‑requested Windows 11 feature is finally coming in 2026 (https://www.windowscentral.com/microsoft/windows-11/windows-11-gaining-movable-taskbar-in-2026)
A long‑requested Windows 11 feature is finally coming in 2026 (https://www.windowscentral.com/microsoft/windows-11/windows-11-gaining-movable-taskbar-in-2026)
- Thread starter
- #166
Finally they listen? LOL. F the users.One for Murray . You have been asking for this and it looks like its in the works.....
A long‑requested Windows 11 feature is finally coming in 2026 (https://www.windowscentral.com/microsoft/windows-11/windows-11-gaining-movable-taskbar-in-2026)
Also be able to change the size . But first you have to prove you aren't a bot ,Finally they listen? LOL. F the users.
- Thread starter
- #168
The image is too blurry. I can't see the colour bands, but I do see 3 stop lights.Also be able to change the size . But first you have to prove you aren't a bot , View attachment 137296lol.
Well worth a look . Great tutorial.
- Thread starter
- #174
Quantum computing?
Meet Quantum cryptography.
Quantum cryptography uses the principles of quantum mechanics, such as entanglement and the no-cloning theorem, to secure data transmission, making it theoretically unhackable. It enables secure key distribution (QKD) where any eavesdropping attempt disturbs the photons, immediately alerting users. This technology is essential for protecting against future quantum computer attacks.
Meet Quantum cryptography.
Quantum cryptography uses the principles of quantum mechanics, such as entanglement and the no-cloning theorem, to secure data transmission, making it theoretically unhackable. It enables secure key distribution (QKD) where any eavesdropping attempt disturbs the photons, immediately alerting users. This technology is essential for protecting against future quantum computer attacks.
Wow. sounds like a game changer.... If anyone understands the game that is... I sure don't but here's the Quantum Cryptography in easy to understand layman's terms.... errrr....maybe not....Enjoy the read.. 
Key Principles
[COLOR=rgba(0, 0, 0, 0.8)]Quantum cryptography relies on several fundamental principles of quantum mechanics:
[COLOR=rgba(0, 0, 0, 0.8)]QKD is the process of using quantum communication to establish a shared key between two parties (commonly referred to as Alice and Bob) without a third party (Eve) learning anything about that key. If Eve tries to intercept the key, the quantum state will be disturbed, and Alice and Bob will notice discrepancies.
Example: BB84 Protocol
The BB84 protocol, proposed by Charles H. Bennett and Gilles Brassard in 1984, is one of the first and most widely used QKD protocols. It involves the following steps:
[COLOR=rgba(0, 0, 0, 0.8)]Quantum cryptography has several practical applications:
[COLOR=rgba(0, 0, 0, 0.8)]Despite its potential, quantum cryptography faces several challenges:
[COLOR=rgba(0, 0, 0, 0.8)]Quantum cryptography offers a promising solution for secure communication by leveraging the principles of quantum mechanics. While it faces challenges in terms of cost and practical implementation, its potential to provide unhackable security makes it a critical area of research and development for the future.[/COLOR]

Quantum Cryptography
[COLOR=rgba(0, 0, 0, 0.8)]Quantum cryptography leverages the principles of quantum mechanics to perform cryptographic tasks, offering a higher level of security compared to classical cryptography. The most well-known application of quantum cryptography is Quantum Key Distribution (QKD), which provides an information-theoretically secure solution to the key exchange problem.Key Principles
[COLOR=rgba(0, 0, 0, 0.8)]Quantum cryptography relies on several fundamental principles of quantum mechanics:
- Uncertainty Principle: The act of measuring a quantum system inevitably alters its state. This principle ensures that any eavesdropping attempt on a quantum communication channel can be detected.
- No-Cloning Theorem: It is impossible to create an exact copy of an unknown quantum state. This prevents an eavesdropper from duplicating the transmitted data without detection.
[COLOR=rgba(0, 0, 0, 0.8)]QKD is the process of using quantum communication to establish a shared key between two parties (commonly referred to as Alice and Bob) without a third party (Eve) learning anything about that key. If Eve tries to intercept the key, the quantum state will be disturbed, and Alice and Bob will notice discrepancies.
Example: BB84 Protocol
The BB84 protocol, proposed by Charles H. Bennett and Gilles Brassard in 1984, is one of the first and most widely used QKD protocols. It involves the following steps:
- Photon Transmission: Alice sends a series of photons polarized in one of four possible states (e.g., vertical, horizontal, diagonal left, diagonal right) to Bob.
- Measurement: Bob randomly chooses a basis (rectilinear or diagonal) to measure each photon.
- Basis Comparison: Alice and Bob publicly compare their chosen bases for each photon. They discard the measurements where their bases do not match.
- Key Generation: The remaining measurements, where the bases match, form the shared secret key.
[COLOR=rgba(0, 0, 0, 0.8)]Quantum cryptography has several practical applications:
- Secure Communications: Governments and military organizations can use QKD to protect sensitive information.
- Financial Transactions: QKD can secure financial data, preventing cybercriminals from intercepting transactions.
- Healthcare: Protecting patient records and medical research data from unauthorized access.
[COLOR=rgba(0, 0, 0, 0.8)]Despite its potential, quantum cryptography faces several challenges:
- Cost: Implementing quantum cryptography requires specialized equipment and infrastructure, making it expensive.
- Distance Limitations: The effectiveness of QKD decreases with distance due to photon attenuation.
- Practical Implementation: Real-world implementation of quantum cryptography is still in its early stages and requires further research and development.
[COLOR=rgba(0, 0, 0, 0.8)]Quantum cryptography offers a promising solution for secure communication by leveraging the principles of quantum mechanics. While it faces challenges in terms of cost and practical implementation, its potential to provide unhackable security makes it a critical area of research and development for the future.[/COLOR]
Superposition......Hard to get your head around.Quantum computing?
Meet Quantum cryptography.
Quantum cryptography uses the principles of quantum mechanics, such as entanglement and the no-cloning theorem, to secure data transmission, making it theoretically unhackable. It enables secure key distribution (QKD) where any eavesdropping attempt disturbs the photons, immediately alerting users. This technology is essential for protecting against future quantum computer attacks.
Interesting because more than once the NSA has caught a hacker and hired them instead of prosecuting them.

About time.....
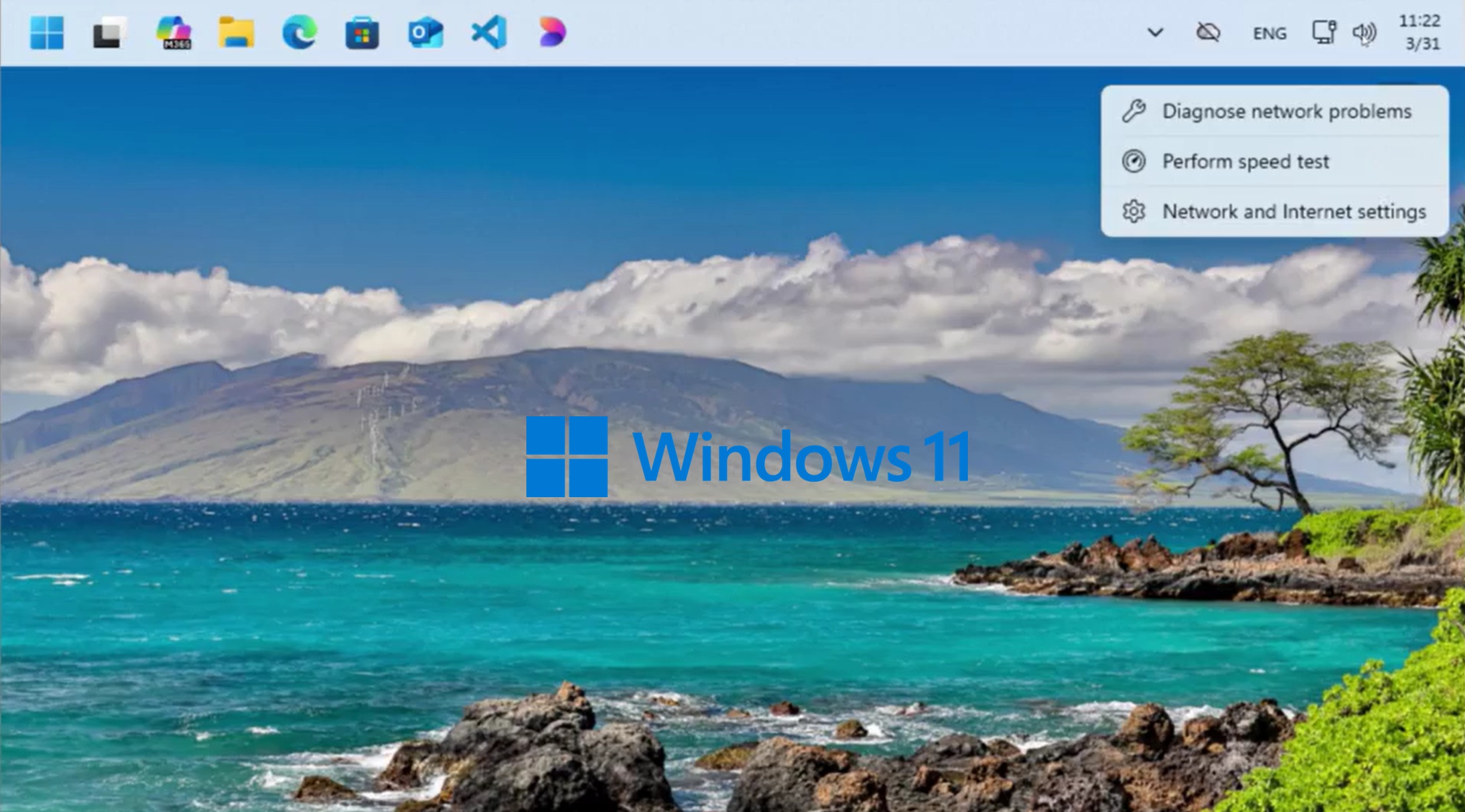
 www.windowslatest.com
www.windowslatest.com
Watch: Microsoft shows off Windows 10-like Windows 11's movable taskbar in action
Microsoft has posted a video showing off the movable taskbar in Windows 11, and it's similar to Windows 10.

I disabled Windows 11's worst defaults in minutes using this free app
Windows Settings app feels like a waste of time.
Users who are viewing this thread
Total: 1 (members: 0, guests: 1)